Your Legacy Dynamics Server is Your Business’s Hidden Security Blind Spot
Is your legacy Dynamics server a security blind spot? Learn why unpatched ERP systems (GP, NAV, AX) are a prime ransomware target and how to protect your critical data.
The biggest cybersecurity threats don’t always come from the outside. But sometimes, they also sit quietly in the server room. While your IT team is busy defending laptops, email, and cloud apps, the old on-premises Dynamics server powering your finances and operations may be wide open to attack.
These legacy ERP systems, like Microsoft Dynamics GP, NAV, SL and AX, were once the backbone of business productivity. But as Microsoft support lifecycles end and security patches stop arriving, they’ve become one of the most dangerous blind spots in the modern enterprise.
This blog explores the Legacy Dynamics security risks that put critical financial, customer, and operational data in jeopardy. You’ll see why outdated ERP servers are prime targets for ransomware and data breaches, how attackers exploit these forgotten systems, and what immediate steps you can take to protect your organization before it’s too late.
Your ERP system isn’t just another piece of business software. It’s the central nervous system of your entire organization, the place where every financial transaction, customer record, inventory update, and operational workflow comes together. If it stops working, your business stops working.
Despite its criticality, the ERP server is often the least protected system in a company’s IT environment. Most security investments go toward defending what’s visible: laptops, email systems, and cloud applications. Meanwhile, the aging Dynamics server, sitting in a back office or a small data closet, quietly runs outdated software, unsupported operating systems, and unpatched databases.
To an attacker, that forgotten server is the ultimate prize. It contains the company’s most sensitive data, operates with elevated permissions, and is usually overlooked in modern security strategies. In many cases, it’s the easiest way into the heart of the business, and once breached, it gives cybercriminals direct access to financial systems, customer information, and operational control.
Ignoring this hidden risk is like locking your front door but leaving the vault open. Your ERP system deserves the same, if not greater, level of protection as your most visible endpoints, because it holds the keys to everything your business relies on.
Many organizations still believe their on-premises Dynamics server is safe simply because it is physically located inside their building. The logic goes something like this: “If it is not connected to the internet, it cannot be hacked.” Unfortunately, that belief has not been true for a long time.
Modern cyberattacks do not rely on breaking through firewalls or sneaking in from the outside. Instead, attackers often gain entry through trusted users and compromised devices. A single phishing email, a stolen credential, or an infected laptop can give them a foothold inside your network. Once they are in, they move laterally quietly, scanning for unpatched systems and vulnerable servers.
That forgotten Dynamics GP, NAV, or AX server running in a back room is an ideal target. It is typically outdated, lacks modern security tools, and is rarely monitored as closely as cloud or endpoint systems. To an attacker already inside your network, it is a wide-open door leading straight to your most valuable business data.
Physical proximity no longer equals protection. Even if your ERP server has never been directly connected to the internet, it is still on the same network as the rest of your systems. So if one user clicks the wrong email, your so-called “air-gapped” server can still become ground zero for a devastating breach.
Once an attacker gets past your perimeter (often through a simple phishing email), they aren’t looking for a fortress; they’re looking for a house of cards. Your legacy Dynamics environment is often exactly that—a stack of interconnected, outdated technologies where a single vulnerability can bring the entire structure down.
Think of your server as three crumbling blocks stacked on top of each other. A weakness in any one layer compromises the entire stack, and attackers know how to find the weakest point.
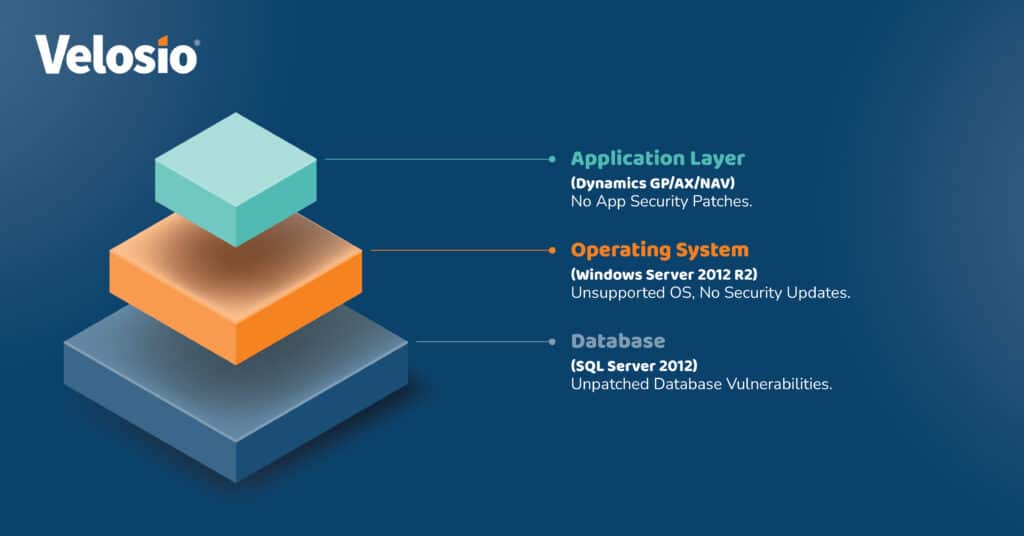
An attacker doesn’t need to defeat all three layers. They just need to find the single weakest crack in the stack—and the whole thing topples, giving them the keys to your financial kingdom.
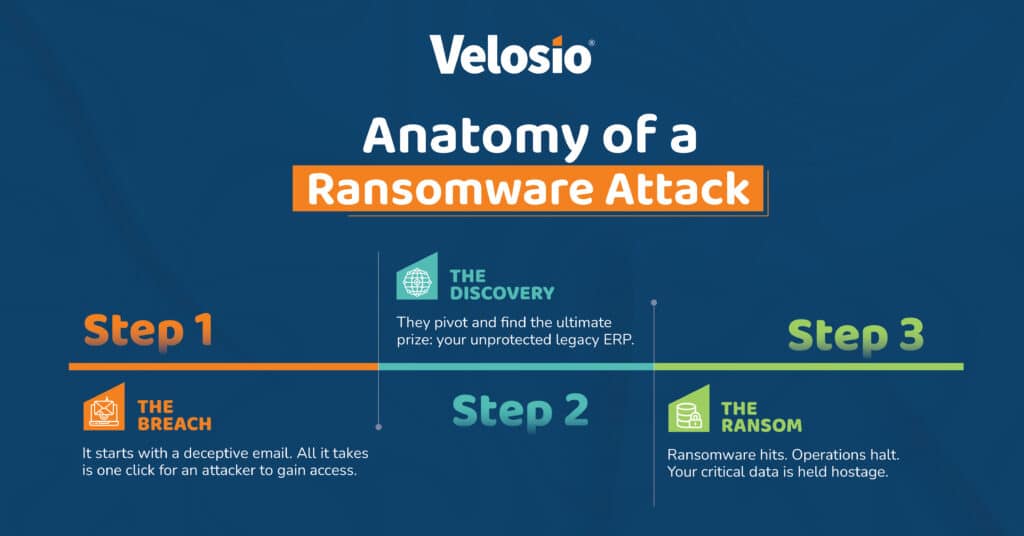
Below is a simple flowchart you can imagine or turn into an infographic. It shows the three predictable steps attackers use against legacy ERP environments, making the threat concrete and easy to explain to stakeholders.
Attackers rarely start by attacking the server directly. They start small: a convincing phishing email, a malicious website, or an infected attachment compromises a user’s workstation. That endpoint often has credentials for internal systems or access to shared network drives. From that user context, attackers install tools or credential harvesters and establish persistent access. Because endpoints are the most commonly used channel for initial compromise, endpoint protection and phishing-resistant controls are the first line of defense.
Once a foothold is established, attackers conduct reconnaissance and lateral movement. They scan the internal network, enumerate services, and look for high-value targets. An unpatched Dynamics server running outdated Windows Server or SQL Server stands out: it often runs services with high privileges, stores financial and customer records, and is rarely monitored with modern telemetry. Attackers exploit weak credentials, misconfigured services, or known vulnerabilities to move from the compromised workstation to the ERP environment, often without triggering traditional alarms.
When attackers reach the ERP server, they look for ways to disrupt, extort, or exfiltrate. A common outcome is ransomware: using an unpatched OS or database vulnerability, the attacker deploys encryption tools that lock down databases and application files. The result is immediate operational paralysis, lost revenue, and a difficult recovery path. In some cases, attackers also steal critical data first, increasing pressure to pay even if backups exist. This final stage is the most damaging and expensive, which is why preventing the earlier steps is essential.
When it comes to protecting your legacy Dynamics environment, you do not need to rip and replace everything overnight. A phased, practical approach can help you reduce risk immediately while setting the stage for long-term transformation. Here is how to stabilize, strengthen, and ultimately eliminate your most serious vulnerabilities.
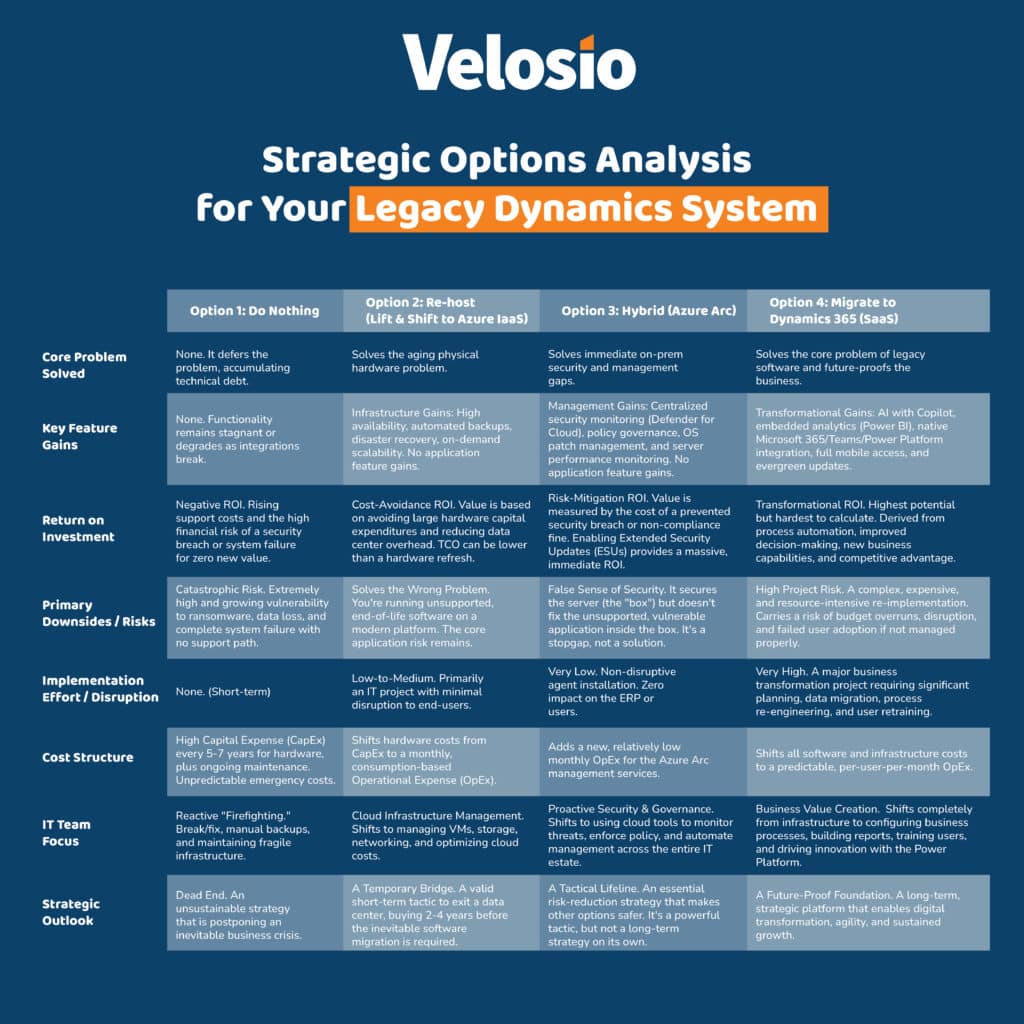
If your Dynamics system still runs on-premises, the fastest and least disruptive way to improve security is by connecting it to Azure Arc. With a lightweight agent installation, Azure Arc brings your local Windows Server under Azure’s centralized management and security controls.
This connection enables your on-premises ERP server to benefit from the same security policies, monitoring, and patch visibility as cloud systems. Most importantly, Azure Arc is now the only method to purchase and deploy Extended Security Updates (ESUs) for Windows Server 2012 R2. These ESUs provide critical patches for vulnerabilities that Microsoft no longer publicly releases, helping you close the most dangerous exposure in your stack while you plan the next step.
Once your ERP environment is stabilized, the next move is to migrate it to Azure Virtual Machines. This “lift and shift” approach transfers your existing Dynamics application, operating system, and database into a secure, enterprise-grade cloud infrastructure.
While your ERP software may still be legacy, it now runs in a modern data center with advanced network security, encryption, and automated backup. Azure’s built-in disaster recovery and high availability options also minimize downtime risk. Most importantly, this move removes your dependency on old, failure-prone physical servers that often lack redundancy or hardware support.
The only true way to eliminate legacy ERP security risks is to modernize completely. Migrating to Microsoft Dynamics 365 transforms your ERP from a vulnerable on-premises application into a secure, continuously updated cloud platform.
With Dynamics 365, Microsoft takes responsibility for security, patching, uptime, and infrastructure management around the clock. Every component, from the application layer to the database, is maintained and protected within Microsoft’s global cloud environment. This means no more end-of-support deadlines, no more manual updates, and no more sleepless nights worrying about ransomware or hardware failures.
Your ERP should be a business strength, not a security risk. Legacy Dynamics systems like GP, NAV, and AX can quietly expose your company to modern cyber threats if left unprotected. By identifying vulnerabilities and taking focused action, you can transform your ERP from a soft target into a secure, resilient foundation for your business.
Your legacy Dynamics ERP may be running smoothly today, but that stability can hide a serious risk. Quantifying how vulnerable your environment actually is can be challenging, especially when multiple systems and versions are involved. That is why we created a quick, interactive 2-minute Security Self-Assessment designed to evaluate your ERP against the most common attack vectors.
This short assessment analyzes factors such as system age, patch status, infrastructure configuration, and exposure points. It then provides a clear security maturity rating along with personalized recommendations to strengthen your defenses.
Ready to turn uncertainty into action? Take the free assessment now to uncover your current security posture and receive a customized roadmap to improve it.
Every week that a legacy ERP remains unpatched or unsupported increases the likelihood of a breach. The costs of ransomware, downtime, data loss, and reputational damage often exceed the investment required to secure or modernize the system in the first place.
Do not wait for a crisis to force the conversation. Schedule a brief consultation to identify your unique risks, prioritize remediation steps, and build a clear, actionable defense plan. The earlier you act, the faster you move from being a vulnerable target to becoming a resilient, future-ready fortress.
Talk to us about how Velosio can help you realize business value faster with end-to-end solutions and cloud services.