When Clouds Turn Bad: A Short Story of Poor Data Governance in the Cloud
What is cloud governance? In short, it’s a set of rules which applies specific policies or principles to the use of cloud computing services.
What is cloud governance? In short, it’s a set of rules which applies specific policies or principles to the use of cloud computing services.
Overall Benefits of a Cloud Governance Program
The following are key benefits of having a solid data governance program:
As digital estates continue to grow in complexity, and organizations adapt to the realities of hybrid work while ramping up their use of cloud architecture, cloud governance is becoming increasingly important and complex. What is cloud governance? In short, it’s a set of rules which applies specific policies or principles to the use of cloud computing services. This model aims to secure applications and data even if located distantly. The best Cloud Governance solutions include People, Processes, and Technology.
You can learn from the mistakes of other organizations who had poor governance in the cloud, leading to overpayment month over month, or worse, a costly security breach. We had the opportunity to help an organization, (who understandably prefers not to be named), migrate to the Microsoft Azure cloud. They engaged us on one aspect of the cloud journey, but they wanted to handle the other aspect. To further complicate things, while migrating to the cloud, they simultaneously divested from another organization. Once the divestiture was complete, and the organization was settled into the cloud, they noticed that their Microsoft Azure footprint and spending was quite large and continuing to surge. The client asked Velosio to analyze consumption and review what was happening from a costing perspective. We assessed the licensing and revisited what they had, asking keys questions such as “is this add-on necessary”? etc.
The cloud is meant to be easy, but sometimes it’s too easy to switch something on that is high cost and resource intensive, driving up cloud costs. The organization in our short story had set something up in the cloud, thinking that they had turned it off, but had some orphaned resources hanging around which were not needed. The same goes for virtual machines – you switch it on, and get rid of it later, but large disks are still out there eating up cost in the cloud.
After identifying areas where the client could cut cloud costs, they now have a better handle on monthly cloud consumption. There are no surprises, and they feel comfortable approving the monthly bill and watching spending month over month. Ideally organizations should know what their monthly spending will be, and if there’s an increase because of added employees, growth, or acquisition, they should anticipate it. If you don’t have the context for a bill increase, complete an audit on the system to determine why – this can save you thousands of dollars in the long run. After all, budgets are only good if they are adhered to.
Other than managing cost and putting a lid on overspend, cloud governance is important for security purposes. One of the biggest concerns about moving into the cloud is security. How much security you need depends on your organization but be sure to activate the built-in security tools your cloud platform provides, from management event logs to account- and region-dependent security rules, to reports and recommendations for account-level security settings.
Velosio (and Microsoft) recommends Zero Trust, least privileged access for users. It’s not that you don’t trust your users, you don’t trust malicious actors trying their hardest to access your data. When your users only have access to the data they need when they need it, it gives them peace of mind that they won’t mistakenly open the door to sensitive data that can be stolen, encrypted, and sold back to you for big bucks. It’s like the old file cabinets we used to use – there were some that anyone could get into, and some file cabinets that were locked up because they held sensitive client or vendor data such as social security numbers, credit card numbers, patent information, etc.
Instead of assuming everything behind the corporate firewall is safe, the Zero Trust model assumes breach and verifies each request as though it originates from an open network. Regardless of where the request originates or what resource it accesses, Zero Trust follows the motto: “never trust, always verify.” Every access request is fully authenticated, authorized, and encrypted before granting access. Micro segmentation and least privileged access principles are applied to minimize lateral movement. Rich intelligence and analytics are utilized to detect and respond to anomalies in real time. Zero Trust authenticates and authorizes based on all available data points, including user identity, location, device health, service or workload, data classification, and anomalies. Does Sharon in IT travel to India and login from the office there twice a year? You can set up rules to expect this type of movement.
A great security posture starts with understanding the threat landscape. Microsoft remains deeply committed to partnering with its user community on sharing intelligence and building a safer world for all together.
You can feel safer with Microsoft Azure because it collects comprehensive telemetry on 43 trillion signals of data and research by more than 8,500 security experts.
Microsoft Defender for Cloud is a Cloud Security Posture Management (CSPM) and Cloud Workload Protection Platform (CWPP) for Azure, on-premises, and multi-cloud (Amazon AWS and Google GCP) resources. Defender for Cloud fills three vital needs as you manage the security of your resources and workloads in the cloud and on-premises:
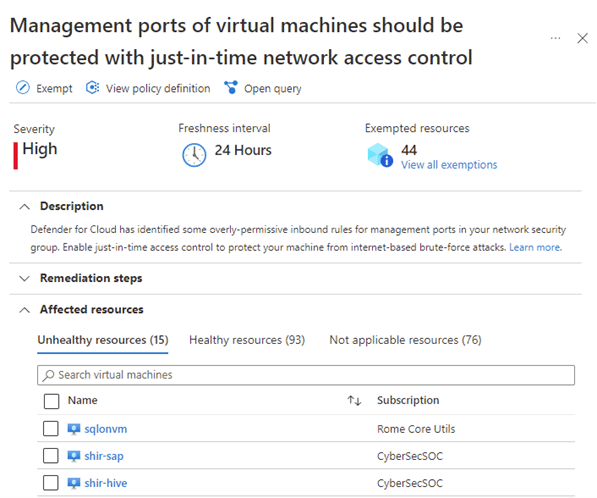
Here is an example of what Microsoft Defender for Cloud looks like:
Additionally, Microsoft Purview provides a unified data governance solution to help manage and govern your on-premises, multi-cloud, and software as a service (SaaS) data. With Microsoft Purview, you can create a holistic, up-to-date map of your data landscape with automated data discovery, sensitive data classification, and end-to-end data lineage. This enables data consumers to access valuable, trustworthy data management.
The Microsoft Purview data map allows you to:
- Automate and manage metadata from hybrid sources.
- Classify data using built-in and custom classifiers and Microsoft Information Protection sensitivity labels.
- Label sensitive data consistently across SQL Server, Azure, Microsoft 365, and Power BI.
- Easily integrate all your data catalogs and systems using Apache Atlas APIs.
Learn more about Microsoft Purview here.
Here’s another short story for you. Velosio’s client had a finance person with amazing Excel sheet. We’re talking pivot tables out the wazoo and hundreds of tabs. The 14-person department heavily relied on this spreadsheet. When the finance person who had developed the spreadsheet left, nobody knew where the spreadsheet was, there was no backup or map to where it was stored. The spreadsheet was so important that the team couldn’t operate without it, so they had no choice but to try to recreate it. This was an impossible task, as it had been created over several years. All this pain could have been eliminated if the spreadsheet had only existed as one version in the cloud. This ensures that it’s not taking up space in multiple iterations in email, chat, server, etc. By storing important documents in the cloud and sending an active link, you have version control and deduplication. Ask yourself – what data do you have that, if it goes away, or no longer becomes valid, or a table is changed, or bad data comes in – may bring your organization down? You don’t want to risk the critical stuff – make sure one copy is in the cloud!! This doesn’t have to be a manual process – Microsoft Purview Data Sharing in the Cloud allows for deduplication. Then, whenever you need to access the relevant data, you get it from a single copy.
Please connect with me on LinkedIn if you have any questions about cloud governance. I’m happy to discuss it with you.
Talk to us about how Velosio can help you realize business value faster with end-to-end solutions and cloud services.